Nobody likes it, so not enough organizations do it. That’s the real takeaway in our report on two-factor authentication. Two-factor authentication (2FA) is an IT security best practice that provides an extra layer of protection for system access, by asking a user for a second means of identification. It is a highly advisable measure to mitigate risk associated unauthorized access, especially in an era of increasing mobility and remote access. And yet, despite these benefits, our annual survey of 34 IT management best practices shows that too few companies apply two-factor authentication formally and consistently.
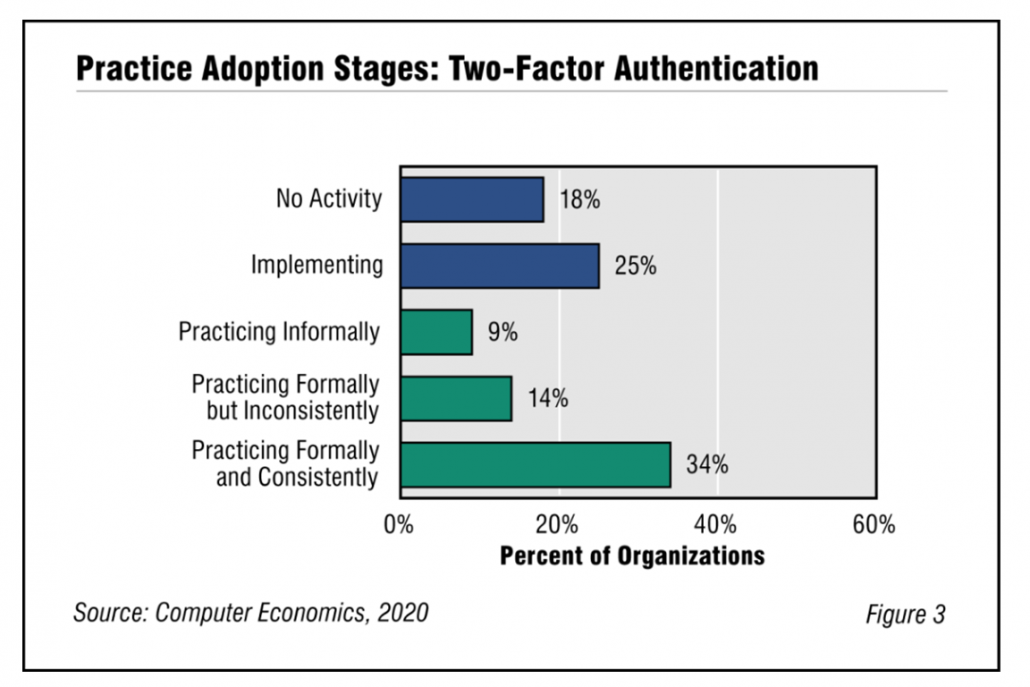
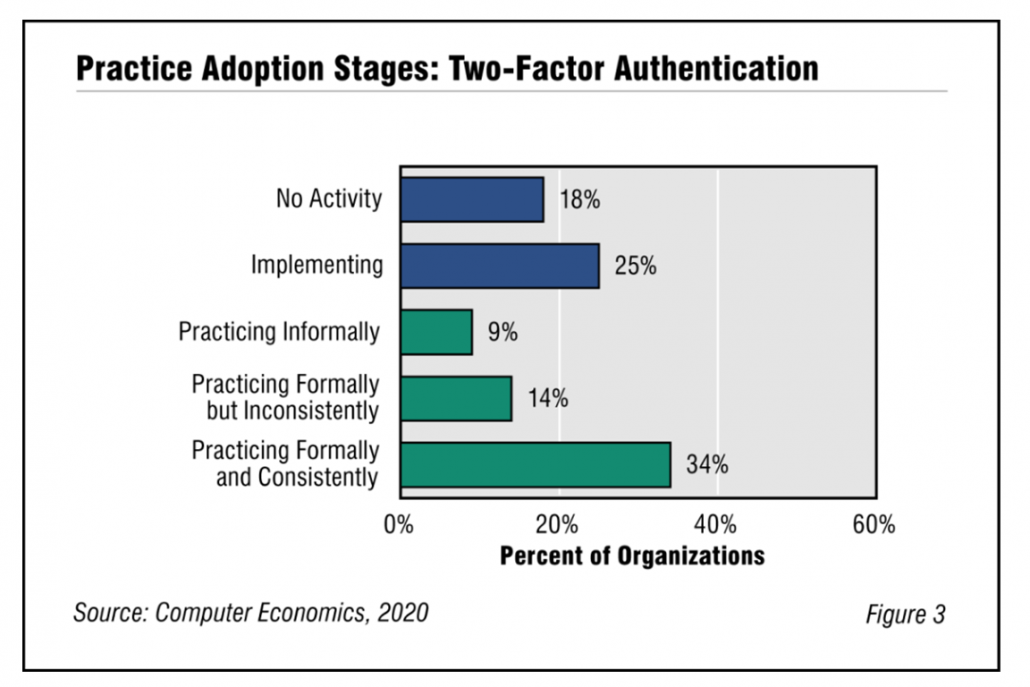
As shown in Figure 3 from our full report, Two-Factor Authentication Adoption and Best Practices, 34% practice 2FA formally and consistently (what we call the maturity level). Another 25% are implementing this best practice for the first time, while 18% report no activity with this practice. The upshot is that 2FA is not applied to the extent that it should be to ensure organizational security.
In addition to username/password, this best practice employs the use of a second authenticating factor, which comes from one of the following three categories (which are explained in full in the full report): something you know, something you have, and something you are. Some forms include answers to secret questions, a code sent to your phone, or one-time password generating tokens.
Why is 2FA needed? Because username and password pairs as authentication factors are as weak as they are ubiquitous. They can be “phished,” stolen, discovered, and cracked in a number of ways. And humans are as bad at making good passwords and changing them regularly as they are at eating their daily requirement of vegetables.
“The big picture is that 2FAis inconvenient, and users just want access ,” said Tom Dunlap, director of research for Computer Economics, an IT research firm based in Irvine, Calif. “Users often rebel against it because the extra layer is seen as onerous or unnecessary. However, that hill needs to be climbed, because companies face a wide array of security and privacy threats and 2FA can go a long way to protecting a company.”
Inconvenience isn’t the only issue. Each form of two-factor authentication has its own weaknesses. For instance, security questions can often be easily guessed and tokens can be lost. This report goes into the strengths and weakness of most major forms of 2FA and suggests practices for making the most of them.
The full report begins with a definition of two-factor authentication. We next study the adoption and practice levels, and examining those by organization size and sector. We conclude with best-practice recommendations.
This Research Byte is a brief overview of our report on this subject, Two-Factor Authentication Adoption and Best Practices. The full report is available at no charge for Avasant Research subscribers, or it may be purchased by non-subscribers directly from our website (click for pricing).