Two-factor authentication (2FA) is a powerful way to improve IT security. But at the same time, workers—and even their managers—often resist it, because it creates an additional step to access systems. As a result, many organizations are inconsistent or informal in their practice of 2FA. That is one of the key takeaways from our new study, IT Management Best Practices.
Two-factor authentication, also called multifactor authentication, is an IT security best practice that provides an extra layer of protection for system access, by asking a user for a second means of identification. It is a highly advisable measure to mitigate risk associated with unauthorized access, especially in an era of increasing mobility, remote access, and hybrid-work environments. But 2FA can frustrate users, who are known for forgetting passwords or losing their 2FA login token. Despite the benefits, our annual survey of 35 best practices shows that too few companies fully embrace 2FA.
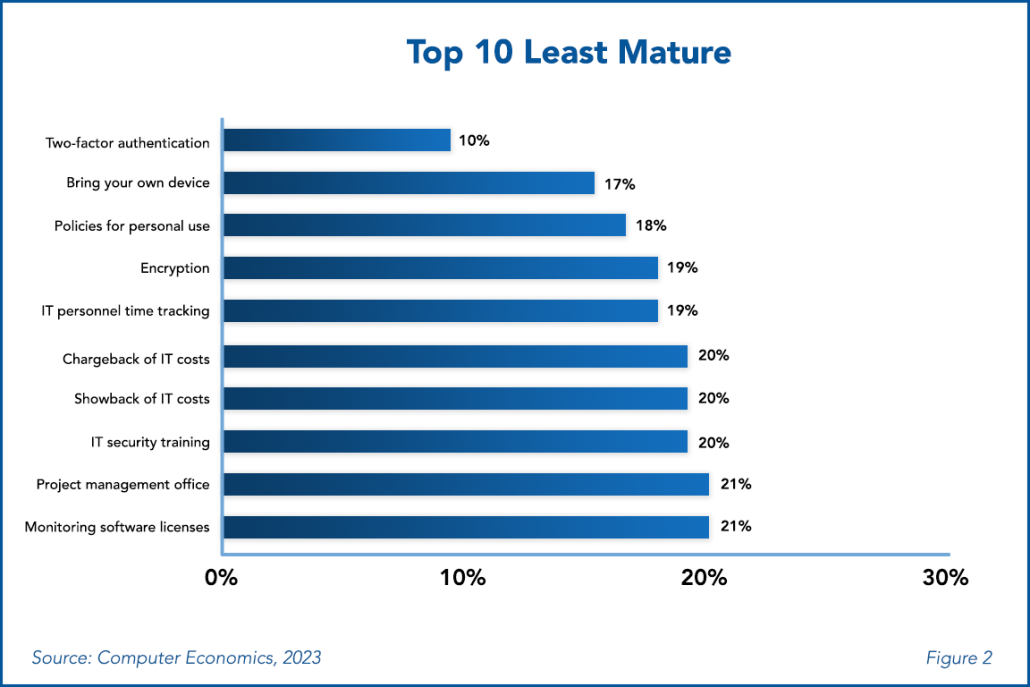
As shown in Figure 2 from our full study, only 10% practice 2FA formally and consistently (what we call the maturity level). In this year’s study, we added two new disciplines: data governance policies and policies for personal use of IT resources. The latter also makes the least-mature list, with a maturity rating of just 18%.
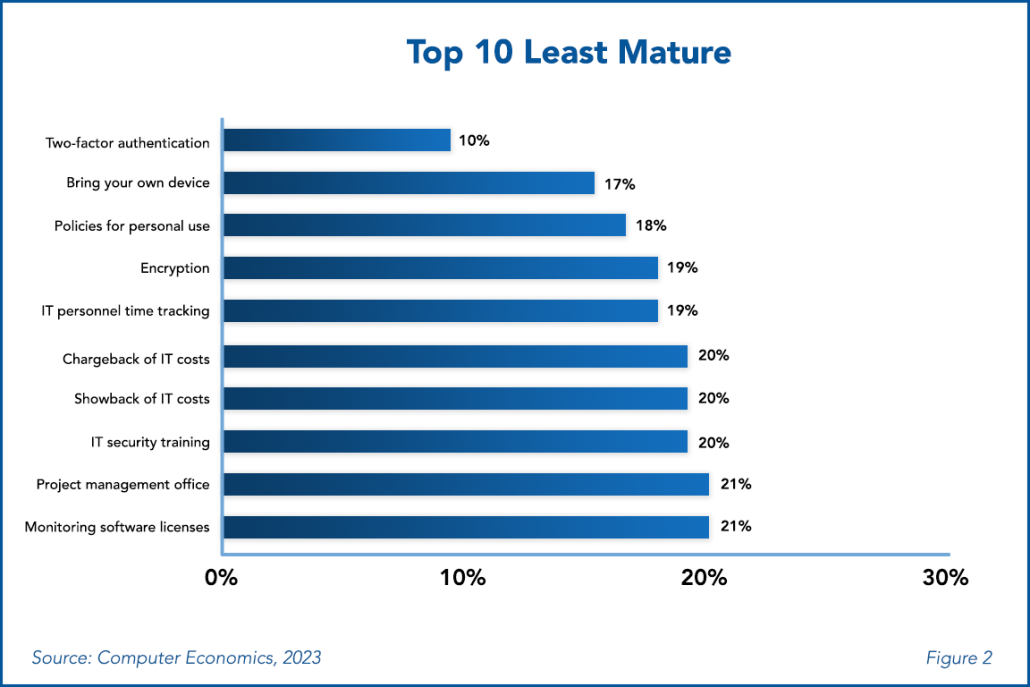
“2FA is again the least-mature best practice in our study, which is surprising, considering the escalating threat level these days,” said Tom Dunlap, director of research for Avasant Research, based in Los Angeles. “In the trade-off between security and convenience, business leaders need to tip the scale back toward security.”
What do we mean by practice maturity? It means the percentage of survey respondents who apply a particular practice formally and consistently. Take IT security training, number eight on our least-mature list, with a 20% maturing rating. Twenty percent of companies formally and consistently mandate IT security training. This means a whopping 80% of survey respondents do not consistently conduct security training. This might mean that these respondents train staff irregularly, without any formal documentation, or perhaps there is no formal training program established. This is quite concerning; IT security training is a relatively easy best practice to implement and can mitigate internal risks. Without a well-designed IT security training program, it opens organizations to unnecessary exposure.
Some of the 35 best practices in our full study are well-established disciplines and are widely accepted. Others are gaining traction among leading-edge organizations. Still, other practices are being widely promoted by tools vendors and consultants but are only rarely adopted, and it remains uncertain whether they will endure. Our goal in this study is to provide IT executives with real-world data on how widely each practice is implemented, a basis for comparing their organizations with their peers, and a means of identifying emerging best practices.
This study is now in its 18th year. Each year, we ask IT organizations in our annual survey to what extent they have adopted a selected list of IT management best practices. Survey participants have five response choices:
-
- No Activity: We are not practicing this discipline in any way.
- Implementing: We are in the process of implementing this best practice.
- Practicing Informally: We do not have formal policies or procedures for this discipline, but we do practice it in an informal or ad-hoc manner.
- Practicing Formally but Inconsistently: We have formal policies and procedures for this discipline, but we do not follow them consistently or to the extent that we should.
- Practicing Formally and Consistently: We have formal policies and procedures for this discipline, and we follow them consistently. This is the maturity level.
The best practices in the study are as follows:
-
- IT governance practices: IT strategic planning, IT project portfolio management, project management office, organizational change management, enterprise architecture, IT vendor governance, cloud governance, and data governance policies.
- IT financial management practices: IT personnel time tracking, service-based cost accounting, chargeback of IT costs, showback of IT costs, IT service catalog, benchmarking IT spending levels, and monitoring software licenses.
- IT operational management practices: IT Infrastructure Library (ITIL), IT asset management system, bring your own device, user satisfaction surveys, and IT performance metrics.
- IT security and risk management practices: IT security training, two-factor authentication, IT security compliance audits, penetration testing, security incident management, encryption, disaster recovery planning, disaster recovery plan testing, business continuity planning, insider risk assessment, and policies for personal use of IT resources.
- Application development practices: agile development, DevOps, website accessibility, and post-implementation audits.
Our full study is designed to increase the awareness of IT leaders concerning what are the best practices in IT management, provide benchmarks against which an IT organization can compare its own adoption and practice level, and justify investments to improve an organization’s IT management practices.
This Research Byte is a brief overview of our report on this subject, IT Management Best Practices. The full report is available at no charge for subscribers, or it may be purchased by non-clients directly from our website (click for pricing).