- Management Consulting
- Strategic Sourcing Consulting
- IT & Digital Transformation Consulting Services
- Business & Process Transformation Consulting Services
- AI Strategy Consulting
- Software Selection Consulting and Vendor Evaluation
- Legal & Transactional Services
- GCC Consulting and Operations
- Vendor Management
- Supply Chain Consulting Services
- Digital Public Infrastructure Consulting
- Procurement Services
- Non-Profit Support Services
- Industries
- Research & Data
- All Reports
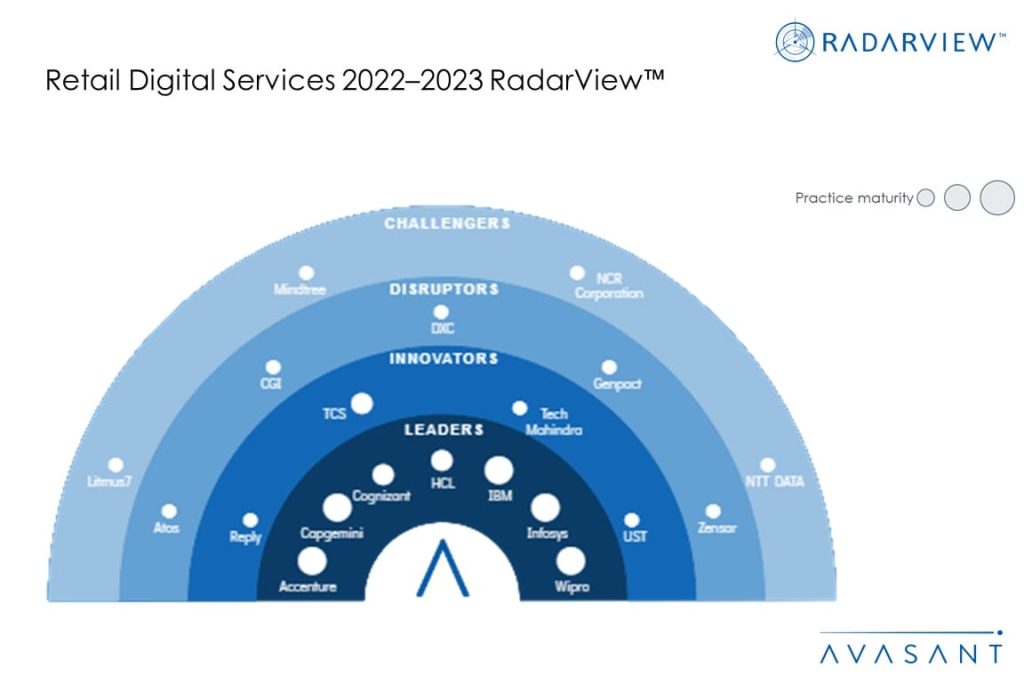
- RadarView™ – Market Assessments
- Business Economics – Human Resources | Finance & Accounting | Procurement Metrics
- Emerging Trends & Predictions
- Avasant Labs
- AvaSense™
- Avasant Copilot
- Global Equations™ Location Intelligence
- IT Spending, Staffing, and Salary Reports
- Computer Economics™ – IT Metrics
- Avasant Tech Innovators
- Industry Economics
- AvaMark™
- Strativa Edge™
- GCC Intelligence
- Benchmarking
- Avasant AI
- Events
- Event Calendar
- Avasant Empowering Beyond Summit 2026
- Avasant Empowering Beyond Executive Roundtable Dubai
- Empowering Beyond Events
- Partner With Avasant Events
- Partner Connect 2025
- Avasant Empowering Beyond Symposium, Bengaluru
- Avasant Foundation Golf Event: Impact the Future 2025
- Executive Spotlight
- About Us
- Contact Us